
Introduction
Best Practices for Protecting Your Digital Assets will offer a comprehensive insight. The digital asset is defined as the “value and ownership of a digital file/document”. Digital assets cannot be completely owned and are not tangible in comparison with physical ones. In other words, if you buy any digital thing, such as a song which you cannot own but simply buy to enjoy. However, you can buy a house and own it too in your name.
With advancements, where protection is increased, the chances of hacks have multiplied. Therefore, one must be extra careful to develop strong passwords along with layer upon layer of protection to secure digital assets. We advise using password generators to come up with strong passwords, which are the first line of defense against any online attack. Remember, always generate strong passwords, although they are hard to remember. Note down at some secure place in case of forgetting. These are always vulnerable and must be vigilant to keep a close eye.
Best Practices for Protecting Your Digital Assets
You must be aware of the fact that what falls in the criteria of digital assets and what does not in your business or brand. For instance, products, apps, websites, and others. We will give you details from which you can learn more about protecting your precious digital assets.

What are Digital Assets?
Digital assets are online assets in digital form owned by one or more owners. Some of these may be present on your or somebody else’s servers. Here are some of the most prominent digital assets:
- Apps
- Photos
- Website
- Intellectual Property
- Social media content
- Company`s registration and other documentation
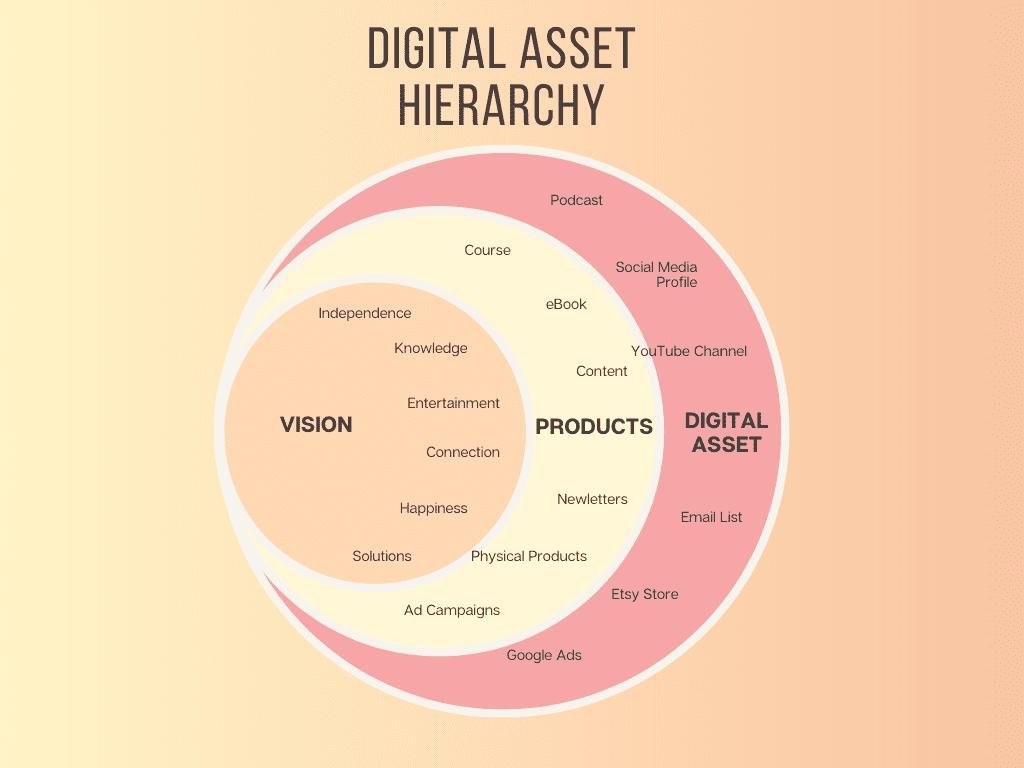
Digital assets are quite important to the overall value of an entity to the investors. These assets could also be sold separately and thus be maintained at maximum protection. Digital assets are as valuable as any other physical asset. Now, let`s move on to comprehend the fact of protecting digital assets.
Companies also opt for Data Management Tools (DAM), which store all the digital assets in an organized form.
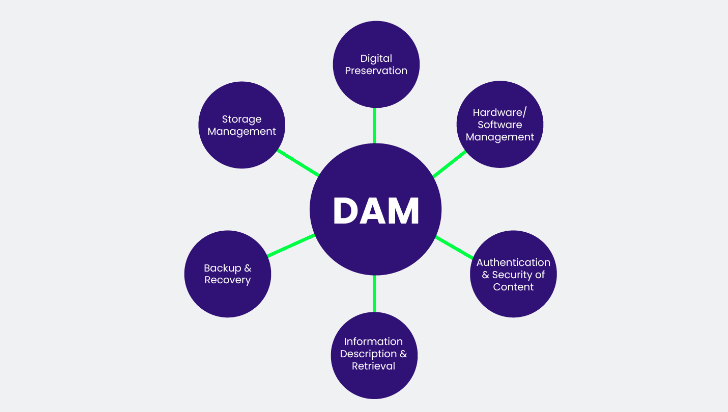
The DAM system can offer you the required information in an instance due to its effective programming. The chances of losing a digital asset are also reduced significantly.
Companies are now enabled with the DAMs to store GBs and GBs of data and access them whenever required. Controlling digital assets along with automation in real-time has become quite easy. In other words, the DAM will store all the previous and new information in an accessible form. Preserving content is its foremost task while covering the gap between different aspects of a company.
How to Protect Digital Assets
Protecting digital assets is quite important as they are pertinent to the very essence of the existence of your company, business, or brand. Digital assets are well-known to hold crucial information about an entity that is quite valuable to be attacked.

If such assets are lost, then chances are that you might recover from the loss. Cybercriminals are always after digital assets that hold value beyond comprehension.
Here are 5 steps to protect your digital assets:
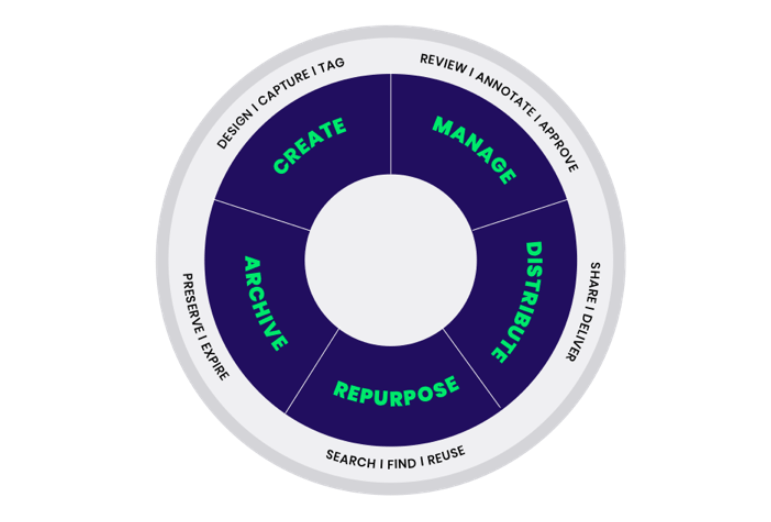
Step 1: List Digital Assets
The initial step is to have complete knowledge of the assets of your company, such as your website, apps, media, and others. Begin listing all your digital assets with modern practices using digital asset management tools.
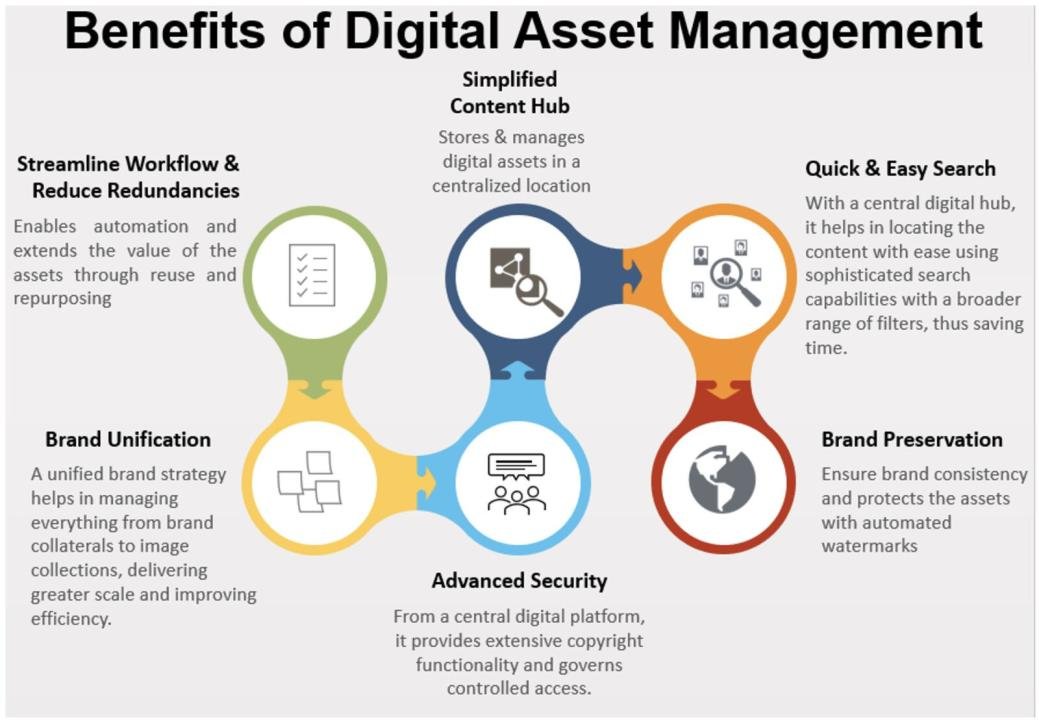
Listing your digital property will streamline your workflow and let you progress much better than before. This will keep things in order while keeping your inventory of digital assets up-to-date.
Step 2: Back Up Your Digital Assets
Having a solid backup system on the Cloud or on physical Servers is of vital importance. You must also store your assets in different locations as a security measure. Also, implement layer upon layer of backups so that in case of any unforeseen situations, you have multiple ways of retrieving your data.

We recommend getting services from any reputed 24/7 IT services in your area. Always choose a company with a good reputation, even if you have to pay some extra bucks, because nothing is more important than the protection of your valuable assets. Additionally, keep your data updated so that while retrieving the data, you can get the latest progress.
Step 3: Cyber Insurance Policy
Invest in a Cyber insurance policy. The idea might sound new to you, but it’s similar to traditional insurance policies, where you have to pay a certain amount to be insured in case of an emergency.

This way, your data/assets will be secure while keeping the financial loss aspect to a minimum.
The insurance policy will cover the cost of your lost assets that might even be worth millions of dollars. This will also prevent your bankruptcy while keeping your business safe and sound. You may choose any solid cyber insurance from any globally reputed company to give you leverage in case of any cyber-attack on your assets.
Step 4: Limited Access & Awareness
Limiting access to your digital assets is one of the best ways to protect your digital assets. In this way, you may offer limited access to 2 or 3 people. In an instance of an event of a cyber-attack, you may pin down the possibilities of information/password leaks. You may also get help from certain applications that will keep you updated whenever someone accesses your digital assets. The chances of digital theft are toned down with limited access.
![]()
Digital assets are not something that must be open to be accessed by a range of different people. This must be as much limited as possible. Additionally, education or awareness to employees is also necessary.
Here it is important to share a fact that “Forty-seven percent of business leaders said human error such as accidental loss of a device or document by an employee had caused a data breach at their organization”. Employees must be well aware that digital assets are of crucial significance and must be dealt with with extreme care.
Step 5: Secure Wi-Fi
Wi-Fi is a need of any household or a big company. Thus, securing the connection is deemed necessary. Hackers usually find the easiest and quickest way to get into your system that is possible through your Wi-Fi signals/connection. Always keep your firewalls up-to-date to thwart any unnecessary intrusion.

Even if your digital assets are present on the Cloud, then reaching from your Wi-Fi could be easier than your imagination. Wi-Fi is also an integral part of any business and easy access to digital assets. Always choose a trusted company and subscribe to the best package to avail of the fastest secure Wi-Fi along with the routers while keeping the data encrypted.
Conclusion
Best Practices for Protecting Your Digital Assets are mentioned in detail. We guarantee that if you follow these modern practices, then your digital assets will remain secure. You may also implement several other practices suitable to your business or company. Keeping your digital assets away from hackers is deemed necessary at all costs. And this process starts with a proper assessment of what asset holds value for your business or company.
Qnnit always recommends investing in trusted and reputed platforms to secure your digital assets. You may also check out [ Easy Fix ] What is the HonHaipr Device on your Wi-Fi Network? Or What is Arris Device? We are always open to your queries and feedback.







